From Hobby Drone to Weaponized Platform: Four Drone Categories Every Team Needs to Be Aware of for Airspace Security Planning
The drone landscape is no longer defined by a single class of threat. What was once a hobbyist pastime now spans a spectrum of platforms with vastly different signatures, capabilities, and operational intent. It’s now crucial that security services understand and account for this variety through clear categorization and appropriate counter-drone efforts.
A Drone Isn’t a Drone
Never assume that ‘a drone is a drone’. Platforms vary widely in capability, signature, and potential uses and behavior. A lightweight consumer quadcopter certainly doesn’t represent the same threat profile as a military-grade loitering munition.
For security teams, being able to make these distinctions is critical, as crafting solid counter-drone strategies without accounting for all drone types may leave gaps in airspace security that can be exploited. The fact remains that drone misclassification is one of the most common points of failure in counter-drone operations and it requires close attention.
Why Drone Threat Categories Matter for Counter-Drone Strategy
Drone threats simply can’t be addressed with a one-size-fits-all model, or by overly relying on basic hobby drone detection methods. Understanding the different types of drones for security planning lays the foundation of an effective counter-drone approach.
A well-defined counter-drone strategy starts with mapping these categories to real-world drone threat types and understanding how detection capabilities differ.
Each category represents different drone detection and defeat challenges:
Signatures: RF, radar, optical, and acoustic output vary significantly
Flight behavior: speed, altitude, and maneuverability differ by platform
Payload capability: determines potential weight bearing capacity
Detectability: some drones are easily identified, others require advanced, layered technology
These differences are especially important when comparing RF vs radar drone detection, where each method performs differently depending on the drone category
Detection architecture should be driven by the hardest-to-detect threat in the operating environment, not the most common. By implementing a comprehensive C-UAS strategy, teams can more accurately classify drone types, improve detection, reduce false positives, and deploy the most appropriate response.
What Are the Four Drone Categories?
What are the main types of drone threats that security teams need to be across?
Consumer (hobby) drones
Prosumer and enterprise drones
DIY and modified drones
Military and weaponized drones
Each category differs in detection complexity, payload capability, and operational risk.
Hobby and consumer drones are easily available and ubiquitous
Category 1: Hobby and Consumer Drones
These retail-level drones, loved by hobbyists and the general public, are everywhere. That’s both the point and the problem. Their ease of accessibility makes them the most common drone encountered in civilian environments, especially around airports, public venues, stadiums, and urban areas.
Consumer drones are typically used for recreation, exploration, basic photography, and travel. For the most part, they aren’t malicious, and their operators don’t have ill intent, but intent isn’t always the deciding factor when it comes to risk. High frequency, low intent absolutely doesn’t equal low risk, especially in congested or regulated airspace.
Typical Characteristics
Inexpensive, highly common, and easily available
Small, lightweight platforms
Limited flight range, battery, and endurance
Restricted payload capacity
Standardized communication protocols
Common Misuse
Privacy and security intrusion
Amateur reconnaissance
Nuisance activity
Accidental or intentional airspace violations
Operational Considerations
Strong and consistent RF signatures
Typically identifiable through known protocols and manufacturer data
High detection reliability using RF-based systems
This makes them the easiest category when evaluating how to detect drones using standard RF-based approaches.
Risk Level
Risk in this category is low to moderate but represents a high frequency of occurrence, especially in civilian environments.
Prosumer and enterprise drones are frequently deployed for legitimate business use but have the potential for misuse
Category 2: Prosumer and Enterprise Drones
This is where the line between legitimate use and potential misuse starts to blur. These platforms represent one of the most operationally ambiguous threat classes where legitimate use and hostile intent often look identical until late in the engagement cycle.
Prosumer and enterprise drones are typically used by organisations for high-end photography and imaging, infrastructure inspection, site mapping, agricultural spraying, and public safety. They can carry decent payloads and are often equipped with advanced sensors and data processing capabilities.
However, the same platform used to inspect infrastructure can just as easily be modified and used for espionage, nefarious payload delivery, smuggling, kinetic attacks, and cyber-attacks.
Typical Characteristics
Common and commercially available
Extended range and flight time
Potential for autonomy
High-resolution optical and thermal sensors
Variable payload capacity
Advanced data processing and AI software
Legitimate Uses
Infrastructure inspection
Surveying and mapping
Media and broadcasting
Security Risks
Persistent surveillance of sensitive locations
Operation at greater distances from the operator
Capability to carry and deliver significant payloads
Cyber-attack potential
Operational Considerations
Detectable via RF, though with increased variability
May operate on modified or less common frequencies
Longer dwell time increases exposure risk
Detection at this level often requires more advanced drone detection methods, particularly when signals deviate from standard protocols.
Risk Level
The threat profile of prosumer and enterprise drones is moderate, with elevated risk when operating near critical infrastructure.
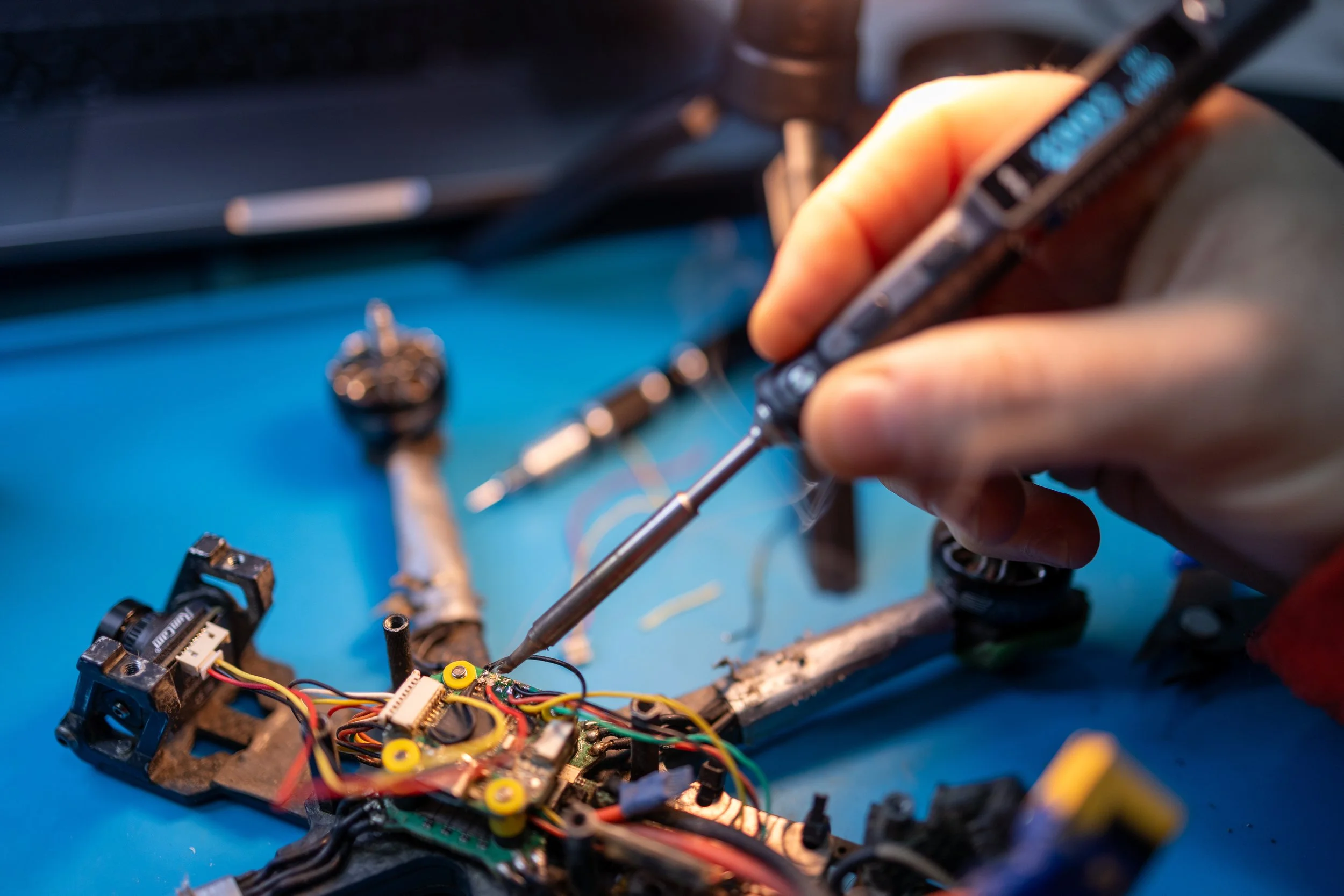
DIY and modified drones are inherently varied and unpredictable
Category 3: DIY and Modified Drones
This category breaks predictability. These are not your typical off-the-shelf drones that operate within parameters that can be expected with commercial and consumer models.
DIY and modified drones are either custom-built or modified with a specific purpose in mind. That purpose isn’t always clear and may well include surveillance, illicit operations, or malicious payload delivery.
Typical Characteristics
Custom-built or heavily modified platforms
Includes FPV racing drones and hybrid systems
Non-standard components and communication links
Threat Profile
Unpredictable payload capacity
High speed and agility
No manufacturer-imposed restrictions
Unpredictable detection issues and evasions
Operational Challenges
Weak, intermittent, or non-standard RF emissions
Absence from manufacturer identification databases
Reduced effectiveness of signature-based detection
These platforms highlight the limitations of traditional approaches and reinforce importance of developing a truly flexible counter drone strategy.
Risk Level
The risk represented by DIY and modified drones is high, due to their inherent unpredictability and potential difficulty in detection.
Military and weaponized drones present an unambiguous threat
Category 4: Military and Weaponized Drones
This category is clear-cut in its high threat profile. These systems are purpose-built for espionage, signal disruption, reconnaissance and warfare, including loitering munitions and tactical unmanned systems. These explicit intentions change everything.
As the name suggests, military and weaponized drones aren’t opportunistic tools, they’re designed to achieve a potentially life-threatening outcome, often with great precision. These platforms are also designed from inception with counter-detection and countermeasure awareness capabilities and represent not only the largest risk but the biggest challenge in terms of detection and defeat.
Typical Characteristics
Larger or specialized platforms
High endurance and operational range
Significant speed and maneuverability
Substantial payload capacity
Threat Profile
Designed for surveillance, targeting, or kinetic engagement
Capable of autonomous or coordinated operation
Applicable across both tactical and strategic scenarios
Operational Considerations
Limited reliance on common RF bands
Reduced detectability using RF-only systems
Requires integration of radar and electro-optical sensors
May call for kinetic defeat responses
Risk Level
The risks presented by military and weaponized drones are very high, with potentially severe consequences, including loss of life and infrastructure damage.
Categorization is not an academic exercise, it directly informs detection architecture, response timelines, and mitigation strategies. What does this mean for airspace security planning?
Aligning Counter-Drone Technology with Threat Categories
Aerial security measures traditionally reflect the specific risk environment, not just the most obvious threat. When designing a counter-drone strategy, security teams often consider variables such as asset criticality, likely drone threat types, and environment.
For example, public venues may primarily face consumer drone threats, critical infrastructure may require protection against modified or weaponized systems, and airports could see the entire threat spectrum. However, focusing too narrowly can still leave vulnerabilities.
How Are Different Drone Types Detected?
Not all drones behave the same, and that’s exactly why detection methods can’t be single modality. The best approach involves tailored detection strategies centered on how different drone categories operate in real-world conditions.
Consumer Drones
Consumer drones are typically detected through their radio frequency (RF) signals, as they rely on standard communication links between the drone and its controller.Prosumer and Enterprise Drones
Prosumer and enterprise drones often feature enhanced transmission systems and longer ranges. They can still be detected via RF, but in some cases, radar systems are also used to track their movement more reliably.DIY and Modified Drones
Custom-built drones present a stronger challenge. Because they don’t follow standard communication patterns, they can often evade RF-only detection. Identifying them usually requires a multi-sensor approach, combining RF, radar, electro-optical/infrared (EO/IR) or acoustic detection to pick up irregular signatures.Military-Grade & Weaponized Drones
These are designed to avoid detection and operate in complex environments. Effective identification typically depends on layered detection systems, integrating RF, radar, EO/IR, acoustic sensors, and advanced data fusion to build a complete situational picture.
Why Single-Sensor Drone Detection Doesn’t Cut It Anymore
Many deployments still rely on a single drone detection method, especially if it’s worked in the past or performs well against the most common drones (such as consumer and enterprise drones). Unfortunately, this approach lacks flexibility and doesn’t amount to a comprehensive CUAS strategy.
The fact remains that no single sensor type can reliably detect all types of drones, and gaps between these technologies are where risk accumulates. This is where layered defense comes into play.
The Modern Necessity of Layered Defense in Airspace Security
Contemporary CUAS strategies now hinge on layered defense (or layered airspace security). Layering creates a tiered approach that integrates multi-sensor detection, identification, tracking, and mitigation into a unified system, often ‘overseen’ by a decision layer such as SensorFusion technology and DroneSentry-C2 AI software. It’s within this decision layer that the data is fused, correlated, and presented to the operator.
Layered defense combines multiple technologies to provide overlapping capabilities for:
Detection: identifying drones using RF, radar, acoustic, or visual sensors
Identification: classifying drone type, signals, and intent
Tracking: monitoring movement, speed, and origin
Mitigation: disrupting or neutralizing the threat
Each layer adds intelligence and redundancy, meaning if one is bypassed, others remain viable.
Why It Matters
A layered approach strengthens counter-drone operations by delivering greater resilience, accuracy, and adaptability. It enables detection of both RF-emitting and autonomous drones, reduces false positives through multi-sensor verification, and can provide continued performance in complex environments.
It’s also modular and highly scalable, making it suitable for everything from critical infrastructure protection to temporary event security.
Designed for Modern Threats
Layered defense is no longer optional for airspace security. It’s essential. By integrating multiple sensors with advanced AI analytics and flexible mitigation options, like DroneShield’s DroneSentry, it enables stronger situational awareness and more effective responses to evolving drone threats.
Preparing for Emerging Drone Threats
Drone technology continues to evolve at a blistering pace, and increasingly outside of traditional manufacturing contexts.
Today we’re seeing an explosion of inventive DIY drones, with advancements in payload delivery, autonomous navigation systems, drone swarms, increased availability of modular components, and open-source flight control systems.
As a whole, the modern drone is increasingly difficult to detect, especially if security is relying on single-modality systems.
To stay ahead of emerging threats, security teams should be looking to scalable and upgradeable layered defense systems informed by continuously updated software.
Future threats are unlikely to arrive neatly labeled. Flexibility and awareness has become just as important as detection capability.
Where to From Here?
Drone threats clearly extend far beyond hobby and consumer platforms. Focusing solely on hobby vs weaponized drones oversimplifies a much broader and more complex landscape that’s forever in flux.
Effective airspace security requires recognition of the full spectrum of drone categories and adoption of a comprehensive, layered approach to counter-drone technology.
Security teams that plan for multiple drone types will be far better positioned to address both current and emerging threats.
Because in practice, the most significant vulnerability in airspace security isn’t the threat that’s detected, but the one that was never accounted for.